Because it’s no longer IF you’re data becomes compromised, it’s WHEN. And for some of us, it’s already too late. But regardless, there’s A LOT you must do to prevent any future abuse…
TOPICS IN THIS GUIDE… ↓(click to jump)
- Proof You’re Data Is Already Online
- Frightful Examples Of What’s Coming
- How To Protect Your Online Privacy
Proof You’re Data Is Already Online
- You’re careful.
- You avoid sharing personal information with strange websites.
- You never fill out those random pop-up surveys.
- You don’t click any suspicious email links.
Sure, you occasionally make online purchases, but only with reputable companies you trust.
Maybe you’ve even bought a virus protection package to prevent malware, spyware, and phishing. But, guess what…it probably doesn’t matter. Sadly complete privacy is a thing of the past.
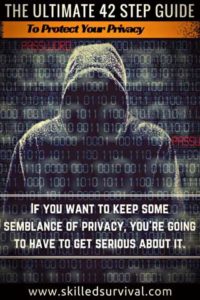
Here’s an example of why I say that: Head over to www.familytreenow.com and you’ll see this:
Enter your first name, last name, and the state most associated with you. Don’t worry; you’re not giving up any new data, you’re just checking to see what this single site knows about you. Now scroll through the results.
See if you can find you. Once you find one that looks like you, click on it and see what comes up.
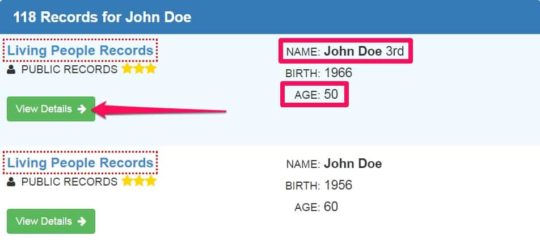
You’ll probably recognize your past home addresses.
How does that make you feel? Violated? Frustrated?
Welcome to the internet age, where even your offline personal data is being uploaded to the web. Then assembled to reveal YOUR personal data to the entire world.
I don’t know about you, but I wasn’t happy to see my results, I never agree with this. I didn’t approve of this. How in the world did my personal information become someone else’s website service? It’s an absolute outrage! And the worst part is we can’t put the cat back in the bag.
This data can never be erased. It’s too late.
So I start asking myself, what’s next? My family, acquaintances, and addresses are bad enough. But when will my internet activity become part of the online universe? On full display for the world to see.
If you want to keep some semblance of privacy, you’re going to have to get serious about it. You need an online privacy plan.
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇Frightful Examples Of What’s To Come…
In no way do I support or condone the website “Ashely Madison” (a website created so married people can cheat on each other). I only use it as an example of what’s already happening.
The site was hacked in 2015, and 40 million customer emails were revealed.
To this day, you can enter any email address (your own, a spouse, a friend, co-worker’s) and see if they were ever on Ashely Madison’s email list. And if you found them on that list your perception of that person would change, right? But what if someone else accidentally typed in the wrong email address (happens all the time) but this time it was YOUR email address?
Or what if someone who dislikes you signs up using your email address out of spite?
Here’s a quote from the Ashley Madison data breach investigation:
“None of the accounts on the website need email verification for the profile to be created, meaning that people often create profiles with fake email addresses, and sometimes people who have similar names accidentally confuse their email address, setting up accounts for the wrong email address.”
– Source [bold sections by Skilled Survival]
How About NSA And The Government?
Let’s take this one step further. What happens when the government has data on who frequents certain websites? It’s not hard to imagine our out-of-control government wanting to know who’s a conservative and who’s a liberal. They could use this data against you (if you’re not on their side).
How? Maybe they decide that conservatives should become targets for IRS tax audits. Actually, we don’t have to imagine this scenario, this stuff is already happening. Remember the 2013 IRS targeting scandal?
Here’s a quote to ponder:
“In early May 2013, the Treasury Inspector General for Tax Administration released an audit report confirming that the IRS used inappropriate criteria to identify potential political cases, including organizations with Tea Party in their names.”
– Source [bold sections by Skilled Survival]
You can’t make this stuff up. We’re quickly approaching an era of no privacy.
And to top it off, every day we hear about new hacks and data breaches from national companies such as Yahoo, Target, Adobe, LinkedIn, Snap Chat, CVS, eBay, Sony, Home Depot, TD Ameritrade, Apple, Facebook, etc., etc., etc.
The list is very long and growing almost daily, click here to see the entire list; it’s eye-opening.
What About Malware and Ransomware?
With the world’s workers going remote in 2020, the ransomware trends have only continued to get worse. A recent survey shows some quite alarming statistics:
- 51% of businesses were hit by ransomware in 2020
- 1/4 of ransomware victims paid the ransom to hackers
- The average ransom demand was $178,000
- The average ransom demand for small businesses was $5,900
- The largest ransom demand was $11.8 million
So What Can You Do To Protect Your Privacy?
While it’s getting harder to protect your privacy 100%, it’s still possible to safeguard much of it. But you can no longer “just be careful” and avoid doing stupid things, you must become proactive.
Here are the detailed steps to protecting your personal privacy.
Home WiFi Network Protection
Let’s start with the network you have the most control over, your home WIFI network. You lock your doors at night, right? You’d never let a stranger waltz right into your kitchen to make a sandwich.
So why would you allow this for your home’s WIFI network? Don’t you know your WIFI signal doesn’t stop at your front door? It often carries out to the street. Unbelievably, it’s estimated that 79% of home routers are at risk of attack.
The last thing you want is a creep parking outside your home to get access to your WIFI and personal network information. So if you haven’t done so yet, lock it down.
Update Your Router Settings
One of the more susceptible areas of your home’s WIFI network is your router. Many people don’t take the time to change the default passwords, change their SSID, turn on encryption, or update their firmware.
1. Grab An Ethernet Cable
The first step to making these critical security improvements is to get your hands on an Ethernet cable. Yes, Ethernet. It’s old school but it’s the safest way to update your router’s firmware (later step).
You want to avoid any connection loss when updating your firmware as this has been known to cause some routers to turn into plastic paperweights. For example,
As one person asks in a Netgear forum: “Can I Update Firmware Without Ethernet Cable To My Computer?”
Answer: “it’s not recommended because there is no real way to determine when WiFi will drop during the upgrade process. You could easily brick your router. Purchase an Ethernet dongle for your laptop. It’s handy to have..”
– Source [bold section by Skilled Survival]
In case you don’t know what the term “brick your router” means, it’s when your router is fried, “done for,” worthless, or destroyed…
2. Log In To Your Router
So once you’ve got your Ethernet cable, physically connect it from your computer to your router. Log in to your router’s backend. For most routers, you can find the backend login screen by typing in the following IP address into your web browser: 192.168.1.1
However, if this doesn’t work, you’ll need to read your router’s owner’s manual to find your router’s IP address. Or you can try going to www.routeripaddress.com and locating your router’s model name to find it.
Your router’s model name will be located somewhere on the device itself.
3. Audit Your Username and Password
Once you’ve accessed your router, it’s time to update your username and password. Never leave these in the default settings. Every hacker (and anyone with basic computer knowledge) knows the standard default passwords for a new router is:
- Username: admin
- Password: admin
If you leave yours like this, sorry to say it, but you’re asking for it. With passwords, the more complex, the better.
That’s why I recommend looking into a password manager (password managers are discussed later).
4. Change The SSID
The next security update is to change your WIFI SSID. Before you freak out, SSID is just a fancy acronym. It stands for Service Set Identifier, but honestly, it’s just the name of your WIFI network.
When you search for WIFI networks, it’s the name you see. That’s it.
When you see a list of available WIFI networks, it’s the names you see. That’s it. But you should change yours from the default. Use something creative so you know it’s yours but not too personal.
Pro Tip: Try using something menacing like “you’ve been hacked” or “this is a virus”.
It helps keep strangers (or cheap neighbors) from trying to connect to your network because who has the courage to connect to a WIFI network called “you’ve been hacked”?
Your friends and relatives may raise an eyebrow when they want to connect to your network but tell them why and they’ll think you’re a genius.
5. Or Hide Your SSID
What’s even better than using scary WIFI network names? Hiding it. Modern routers let you adjust this setting. Turn it on and your SSID won’t show up at all in WIFI network searches.
The good news is: Your computers and devices that are already set up and connected will be fine. It’ll only be a hassle when you want to connect a new device (smartphone, smart TV, etc.).
When this happens you can either type in the SSID info manually in the setup step (since you won’t see it). Or you can go back into your router, allow the SSID to display, connect and then hide the SSID again.
Is this a pain in the butt? Of course, but if you want to protect your security and privacy that’s what it takes in today’s world. Get used to it.
6. Double-Check Your Encryption Settings
Now it’s time to embrace encryption. Another jargon term but necessary to understand and use. Without getting too technical, you need to switch from WEP to WPA2-AES and disable the PIN method of using WPS.
You want to use WPA2-AES because it’s the newest and strongest form of encryption. That’s all you really need to know.
If you can’t enable WPA2-AES encryption because your devices are too old then it means you’re long overdue for new devices (computers and routers).
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇7. Check For Firmware Updates
The next step in your router security adventure is to check and update your firmware. New security breaches occur almost daily. So to combat these new breaches, router companies periodically push out new firmware updates.
These firmware updates patch new security holes. However, if you’ve never updated your firmware there’s a good chance you have security holes. And this is not a one-and-done task. You should check and update your router’s firmware on a set schedule.
Once a year will work for most people. Normally, on the login screen, you’ll see a “check firmware” button. Click it, follow the prompts, and update to the latest version.
8. More Router Setting Changes
A couple more router security tips to consider: Do you plan to ever change your router settings when you’re far away from home? Probably not. Do you want someone else to have the ability to change your router settings remotely? Hell no!
So go ahead and turn remote management off. Look for something named Remote Management, Remote Access, or Remote Administration settings.
Now since we’re talking about remote management, why don’t you go ahead and just turn your WIFI off when you’re out of town?
Unless you have devices such as a WIFI doorbell or a NEST learning thermostat (that uses the internet while you’re away), you might as well turn it off while on vacation.
9. Time For A New Router?
If your router is too old to make these adjustments, it’s time for a new one.
The good news is: That a new router can significantly increase your data speeds. I personally upgraded my router about two years ago and it was money very well spent.
Before upgrading I was struggling to stream any video content, now it’s coming in at HD levels with no problem. This might not be your issue but it was for me.
If you decide to get a new router skip 802.11b or 802.11g and make sure it follows the newer, faster 802.11ac standard. You are now no longer a part of the masses with unsecured routers. Congrats!
Computer Setting For Privacy
Once you’ve got your router on lockdown, it’s time to focus on your computer and online settings. I’ll start with one of the most important privacy and security actions: your passwords.
10. Use A Password Manager
This one changed my life. Everyone should become a LastPass user. The FREE plan allows you to manage all your desktop passwords.
And for only $12 per year for their premium option, such as family sharing and priority support. Here are the main reasons you need LastPass:
- Only need to remember 1 password to login to all your sites
- Start creating high-security super complex passwords
- Use unique passwords for every site
- Autofill’s in your email and passwords; if you so choose
- All password data is encrypted (which means your passwords can only be seen by you)
- You can add 2-step authentication to drastically increase the security (more details on 2-step authentication later).
If you’re like me and have lots of sites and passwords, you need a password manager in your corner.
LastPass is trustworthy, protects you and your data, and improves your online privacy from all the bad actors out there. If you’re still using simple (easy to crack) passwords like “Steve12” or “Rover1” or even “ihatemyjob” you are at high risk.
Instead, use LastPass to create complex (very difficult to crack) passwords that look more like this “fL3&sE$^tW$z#”, and start sleeping better at night.
11. Your Gadgets Are Spying On You
Does your computer or smartphone have a camera built-in? Or a desktop webcam? Then you should know it can be used to spy on you.
One word comes to mind; creepy. Imagine someone watching through your open laptop. Probably recording what they see. Malicious actors can turn on your cameras and watch your every move.
Here’s a small news snippet about one such creep:
In all, Mijangos unlawfully accessed and could control more than 100 computers.
He read their emails, watched them through webcams without their knowledge and most damaging was his discovery of nude photos they had taken of themselves. Mijangos then threatened to post the images online unless his victims were willing to provide more racy photos or videos to him or if they went to police, according to court documents.
– Source – [bold sections by Skilled Survival]
What’s even worst is most of Mijangos victims were teenage girls.
The archive of voyeurism was staggering: over 15,000 webcam-video captures, 900 audio recordings, 13,000 screen captures. In total, he had infiltrated more than 230 victims, including juveniles.
– Source [bold sections by Skilled Survival]
The only good news it’s an easy problem to solve and you don’t need high-tech software to protect your privacy from this invasion. You just need a sticker. Place a webcam sticker over the camera when not in use and voila, problem solved.
Focus On Your Browsers
Web browsers are in the business of making money. The searcher (you) is the product, the advertisers are the customer. The more people who use a specific browser the more money they make on ads. And advertisers always want to know more about YOU.
So browsers, by default, are not set up with a high level of private security.
This is a shame, so you have to take proactive action to protect your online browsing privacy. Here’s how:
12. Check Links Before You Click
Don’t be a click-happy-nincompoop. If an online or email link seem sketchy, trust your gut, it’s probably not safe. But if you still want to click it, check it first.
You’ll need to copy the link without clicking the link. Hover your mouse’s pointer over the link and the address will display in the bottom corner of your browser.
Now, right-click on the link to access the drop-down menu. Copy the link address. Now head over to urlvoid.com. Paste the copied address into their search bar. Click the scan button and see what comes up.
Is this foolproof? Absolutely not. But it’s better than clicking blind.
13. Add HTTPS
Websites that use HTTPS means they encrypt the data that travels back and forth between their website and your computer. Unfortunately, this newer standard is difficult to implement and so is not yet widespread.
You can tell if a site is using HTTPS if its web address starts with it, as opposed to starting with the old “HTTP” standard (notice no “S’ at the end – the “S” stand for secure).
While it’s currently impossible to avoid all sites that don’t have the new standard yet, you can do yourself a favor and add an extension to help.
Download the HTTPS Everywhere extension from Electronic Frontier Foundation.
This will ensure your connections will be encrypted anytime you connect a website that supports the HTTPS standard. It works with Chrome, Firefox, and
14. Block Ads
We’ve come a long way from old-school billboards and commercials. While most ads suck, the online sort can be more than just annoying. They often snoop on your online activities without your consent.
Consider adding an ad-blocking extension such as Adblock Plus, Disconnect, Privacy Badger, or UBlock.
15. Make G Behave or Ditch Them All Together
G owns search. They dominate the market by a massive margin, with over 60% of U.S. searches. And once people develop a habit of using it they keep using it. No matter what the privacy setting is.
So I have 2 suggestions for you.
16. Meet “Duck Duck Go”
The first and most surefire way to protect your online search history and data is to use Duck Duck Go. Weird name a for search engine, but they are the “bee’s knees” when it comes to search privacy.
Think simple, spam-free search results without sketchy stuff. Minus recording your IP address. Minus tracking cookies. No personal information was collected. No personal information was shared.
Just glorious search engine privacy. You’re welcome.
Note: I’ve recently changed to using Brave as my privacy browser of choice.
17. Restrict the Big G
Alright for everyone who can get off the G train cold turkey, then you should still limit their data collection. Honestly, for as big and dominant as G is they do provide a good amount of privacy control. But not by default. For the most part, it’s up to you to turn it off and restrict it.
So go to My Account to control what data you agree to be collected and how it’s shared. Specifically, go to Personal Info & Privacy to review Location, Search, and YouTube Search History. Feel free to delete all your history at once or one item at a time.
Also, make sure to prevent G from recording your private data going forward.
18. Ditch G For Good?
You can delete your G account if you want to go hardcore. This option cannot be undone. So make sure you are ready for it.
Go to My Account or Services, find the “cancel my account” option, take a deep breath, and follow the prompts.
Again, you will lose all your G account data (old emails, calendar, history, G+ data, etc.) going this route so don’t do it unless you’re 100% ready.
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇19. Wearables (a.k.a. Spyables)
Most wearable fitness-based devices (such as Fitbit) use Bluetooth technology to connect to your smartphone. However, Bluetooth is not secure. It’s fairly easy for data access “sniffers” to nab the data being transferred.
Data such as a user’s name, password, address, and GPS. Not the sort of information you want tech-savvy strangers to know.
So go low-tech and turn off your Bluetooth syncing while you’re away from home. Then turn it back on once you get home. Data that are not being broadcast can’t be snatched out of the air.
Problem solved (plus, the battery life of your wearable and phone will improve).
Protect Yourself From Ransomware
Ransomware is alive and well. Hackers are making a fantastic living by blackmailing innocent people with their own data. The way ransomware works is a hacker either steals a person’s data or takes over their computer.
Then they contact the victim and demand money to save the data from destruction (or the sharing of personal data).
If it’s data that you would hate to lose or data that you would be ashamed to share, they use this as leverage (i.e. blackmail) to get you to pay up…or else. Scary stuff. And it’s growing in popularity.
“On average, Ransomware infects 30,000 to 35,000 devices in a month.” – Source
That’s a whole lot of misery for hundreds of thousands of people each year. And the frequency of attacks and the number of “dollars” demanded are both rising at incredible rates.
It’s only a matter of time before you (or someone you know) are affected. Notice I used “dollars” in quotes above, that’s because often ransomware hackers demand getting paid in cryptocurrencies like bitcoin.
Side note: If you’re going to own any cryptocurrencies, you’re going to want to store them in a hardware wallet to keep them safe from hackers stealing them from you.
On a personal note, I have a friend who’s Dad’s data was held hostage via ransomware. Get ahead of this before you’re a victim too. You need to:
- Back-Up Your Data
- Keep Software Programs Up To Date
- Use Data Encryption
20. Back Up Your Data
Use a storage system that backs up all your important files and data automatically. That way, if you’re ever hit with ransomware, you’ll be able to restore your files without having to succumb to these scums’ demands.
Here’s an extensive backup guide to help get you started. As you’ll discover in the guide you have 3 backup options to consider: bootable, external, or cloud. The choice is yours.
21. Keep your Software Up To Date
Set your computer and phone to update software automatically. This will make certain that you don’t have any unnecessary old security software loopholes. When a new security patch is pushed out, you will get it ASAP.
Use Data Encryption
Encryption is for everyone. Nearly everyone uses encryption every day. But few people even understand what it is. Encryption is the act of scrambling data from sender to receiver.
If someone sees the scrambled encrypted data during transmission, it looks nonsensical to them. Unless they have the encryption key. The key takes the scrambled information and unscrambles it.
Another example: Let’s imagine there are 3 people in a room and only 2 of these people know Morse code.
The 2 people who know Morse code start tapping back and forth, laughing and pointing, etc. (they know the key) but the third person is clueless. The data being transmitted (long and short taps) is encrypted as far as the third person is concerned.
So encryption scrambles your digital data so it’s unreadable to anyone who doesn’t have permission to access it. Without encryption, online purchases would be impossible since you’d be sharing your credit card information with the entire world.
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇22. Encrypt Your Smartphone
Your smartphone knows nearly everything about you. With GPS, it knows where you are all day long (assuming you take it with you). It knows who you called, what websites you visit, who you text with, what you said, etc.
The good news is most smartphones today have encryption available. You just need to take the time to enable it…
Look in your phone’s settings and find the Security option (it may be called something else on your phone). Then look for the Encryption option. Now follow the prompts.
23. Encrypt Your Computers
You can encrypt your entire computer’s hard drive or just specific sensitive files. The step to enabling encryption on your computer is different from PC or Mac and it also depends on the OS version.
Here’s an article that will help you get started in figuring out how to encrypt your computer’s hard drive system.
24. Encrypt Your USB Drives
USB drives get misplaced. So you’d hate to accidentally leave it laying around only to have a stranger plug it in and go through your data.
You should get an Apricorn flash drive with built-in encryption. They cost a few dollars more but consider it a single-fee insurance policy to protect your data.
25. Encrypt Your Cloud Data
Some folks are worried about storing their data in the cloud. And I don’t blame them. You are giving up a lot of control of your data for convenience.
You’re essentially allowing your data to be stored at a remote server somewhere. However, for some, convenience is worth the risk.
For example:
With small businesses or for a long-distance family, the cloud makes sharing data and photos much easier. So if you decide you want to use the cloud you must
- Avoid uploading your most sensitive information
- Make sure it’s encrypted
Dropbox is a popular cloud-based application that provides data encryption.
I’m sure there are others but make certain you do your research and turn the encryption option ON if it’s not ON by default. You should also only choose a cloud-based Storage Company that supports 2 step authentication.
26. 2 Step Authentication
- Is the cloud convenient? Yes.
- Does it use data encryption? Maybe.
- Does it have 2 step authentication? It better, or you shouldn’t use it.
Most cloud-based storage companies tout their data encryption tactics. And as long as you use a strong secure password and 2 step authentication, you’ll significantly lower the risks of an intruder gaining access.
So what’s 2 step authentication? It’s basically a second form of proving you are, who-you-say-you-are. The first step is your password. But as we all know, passwords can be hacked (especially if they are simple and short).
But by adding a second “step” of authentication, you’re dramatically reducing the chances of your accounts being compromised. With 2-step-auth enabled, not only does a hacker have to brute force cracked your password. But they now must also have your 2nd authentication code as well.
This hacker headache alone makes it not worth the time to pursue your accounts.
The most common way 2 Step Authentication works is to either send an SMS text of the code to your phone (or through an app) that generates unique codes every minute.
The bottom line is:
When you enable 2 step authentication on your accounts, you’ll start by logging in as normal and instead of gaining immediate access, you’ll have to enter a unique code.
Depending on the account, the code may be sent to your phone via text or you might be able to get the code through an app. You enter the unique, time-limited, code, and then you get access to your account.
A bit of a pain? Yes. Worth it? Yes.
Your best privacy option is to either avoid using cloud storage or only use it for data you wouldn’t mind the entire world seeing. This takes us to the next topic…
Stop Over-Sharing
27. GPS Tracking
Most phone apps (especially popular ones like Facebook) by default track your GPS data.
With some apps, you can turn off this function, and you should. And if you can’t turn off the function, then I suggest you remove the app from your phone entirely.
The other option is to turn off your phone’s GPS and only turn it back on when you are actually using it for navigation purposes. No one needs to know where I’m at, or where I’ve been, period.
28. Turn On Log In Approvals
“Log In Approvals” is just Facebook’s version of 2 step authentication. This means even if someone steals or guesses your password, they would also need a unique code to get in. Making it much less likely.
So turn on “login approvals” to lock down your Facebook account. You can find the setting in your Facebook account settings area.
29. Become Elusive
Maybe you’re not interested in having an old high school crush looking you up on Facebook and friending you. So what’s the best way to avoid this awkward fate? Hide.
You have the option to show up in the Facebook search results or not. Go to the “who can look me up?” settings section on Facebook. But like most privacy settings, by default, you will show up in the search.
So you have to be proactive and turn that setting off.
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇Protection On Public WIFI
Many people enjoy connecting to free public WIFI at places like Starbucks.
Just find the network, accept the terms, and start surfing. But did you decide to automatically connect to that network whenever it’s in range for future convenience? Oops. Because what if a hacker creates a WIFI network that sounds like Starbucks ‘ official one?
Maybe the real Starbucks connection was named “WIFI Starbucks,” and the hacker created a rogue WIFI called “Starbucks Official.” You wouldn’t know which one was the safe WIFI, so you connect to the wrong one; oops, you’ve just been hacked.
You can combat this by asking the Starbucks staff (or whichever business you’re visiting) which WIFI is legit and never allowing your computer to automatically connect to public WIFI.
Also, never conduct sensitive affairs on public WIFI networks, such as logging into bank accounts.
30. Enable Your Computer’s Firewall
A computer firewall acts as a front door for your computer. It won’t automatically let outside computers link to yours without your permission. Just as you would leave your front door open for anyone to walk into your home.
Go to your computer’s security settings and double-check that it’s enabled.
31. Hide Your Computer
Once your firewall is enabled go a step further and cloak your computer. If the bad guys can’t find you, then they can’t hurt you.
- On a PC, it’s normally under Advanced Sharing settings.
- With a Mac, you can enter stealth mode in your firewall options.
32. Use The Automatic Options
Whenever you decide you want to join a public network, make sure you classify it as one. You can classify any network you connect to as “home” or “public”.
When you classify it as “public” your operating system will forget the network when you log off. These terms and options are for PCs. For a Mac, use the free-to-download Control Plane app.
33. Use A Virtual Private Network
In my opinion, this is the most crucial step to protecting your privacy when browsing online in public or private! “Incognito” windows don’t record your online history in your browser but that’s about it. Your computer’s IP address still shows where you’ve been online.
A Virtual Private Network (or VPN for short) is a simple but effective online privacy tool. A VPN routes your internet connection through a remote server. So all of your internet activities are not tied back to you or your computer.
- Without A VPN: You’re Computer —–> Websites
- With A VPN: You’re Computer —–> Virtual Server —–> Websites
All computers have a unique address called an IP address. When you visit a website, you’re essentially leaving your computer’s IP address at the front door. However, if you route your connection through a VPN you don’t leave YOUR IP address at the front door, you leave the VPN’s IP address. And the VPN’s address is not tied back to your IP address, so it lets you surf the web anonymously. Genius!
Without the VPN anyone with a bit of technical know-how can see which sites you visit and how often. However, with a VPN your information and privacy are protected.
Unfortunately, with a VPN you get what you pay for. And you can’t trust any old fly-by-night VPN operation. I recommend Using Hide My Ass
That’s why I recommend HMA. They were founded in 2005, they have thousands of remote servers, they encrypt all the data, and I’ve been a satisfied customer since 2012. They are worth every penny to help protect my online privacy. Never go online without it.
34. Go Long and Short
Always, always, lock your mobile phone screen. The FCC estimates that about 1 million smartphones are stolen each year. And if you’re like most Americans, you keep a boatload of sensitive and personal information on this device. And often, out of convenience, your apps are set to automatically keep you signed in.
So with a single tap, you get full to access your personal accounts (without having to enter an email or password). This is the typical setup for your Facebook app, Twitter app, Dropbox app, etc.
Are you OK with a thief having unfettered access to these accounts? I didn’t think so. The best way to protect your smartphone’s data is to make your pin code or finger swipe code longer and more complex.
Don’t get lazy and use a common pin code like 1234, 0000, 1111, 2222, etc. In a recent pin code data study conducted by datagenetics.com they discovered:
The most popular password is 1234…
…it’s staggering how popular this password appears to be. Utterly staggering at the lack of imagination...
…nearly 11% of the 3.4 million passwords are 1234!!!
If any of these easy combinations sound like your pin. Do yourself a favor and change it to something random or even better yet, go with a 6-pin random code for even more security.
Smartphone thieves will attempt all the obvious combinations first and if your pin is one of these they will get in. If it’s not an obvious code they will eventually give up.
Now Go Short
Now, a pin code is utterly useless if you have a super long screen timeout.
The good news is: You can change this setting. You can choose from “immediate timeout” all the way to “never timeout”.
The bottom line is: The shorter the better. I recommend having it set to immediate timeout for the highest amount of security.
Sure it’s a bit of a hassle to have your screen locked while in the middle of reading an article. But this will prevent a thief from having hours and hours of access to your smartphone data.
If your phone auto locks in under a minute, then chances are a thief will never get easy access to your data from the start.
Protect Your Snail Mail
35. Avoid The Phishing Nets
You’ve probably heard of the term phishing. It’s those real-sounding emails that are sent in an attempt to get you to click a link and share information. Oftentimes these emails look authentic.
They pretend to be from a company you use asking you to “update your password”. But they are really phishing for your password by asking you to change it. Once they have your password and can get into your account.
The easiest way to stay safe from these sorts of attacks is to use two-factor authentication. This prevents anyone with just your password from accessing your accounts.
They would need the 2nd factor as well (see the prior section on two-factor authentication).
36. Be Skeptical Of All Emails
Nowadays, most legit companies don’t ask you to click links in emails to update passwords. But if you’re ever uncertain, you can always open up a new browser window and type in the URL that’s displayed; bypassing having to click the link.
Links can say one thing but do another.
Or they can redirect from one location to another. So click all links with a healthy dose of skepticism.
37. Pick Up The Phone
Again, one of the best ways to avoid these new-aged scams is to not play the game. Pick up a phone and call the company. Ask them about the email you got.
This will provide the proof you need to find out if the email was legitimate or not.
38. Use 10-Minute Email
Occasionally, you are willing to trade your email address for access to a website, to sign up for a loyalty card, or to get an email receipt. But what if you only want the one-time service and don’t really want to give up your real email address?
Use www.10minnutemail.com instead.
This service allows you to create an email address that is only functional for 10 minutes (or 20 if you choose). After that time is up, the email address self-destructs and 10minutemail doesn’t retain any personal data. Just be aware, you won’t have access to any follow emails from the company.
So only use the 10-minute email option with companies you don’t trust. You don’t want to miss out if they’re sending you emails you actually want.
39. See Who “Sharing” Your Email
Don’t you hate when you get an email from some random spammer? Doesn’t isn’t it frustrating you don’t know which company gave away your data to that spammer?
Start using this neat trick to find out who the original a$$hole was. If you have a Gmail account, Type “+” “websitename” before the @ symbol.
For example: If your Gmail address was test@gmail.com and you signed up with XYZ Company, you’d submit your email address as test+XYZ@gmail.com
Now all emails from the XYZ company will still go to your email address but will now include some extra info. So if you ever get spam emails from a random company you’ve never heard of, you’ll know who sold your privacy down the river.
Want a free 78 item preppers checklist?
Enter your email below to instantly download this Complete Checklist PDF. No purchase necessary. 👇 👇40. Shred Sensitive Snail Mail Documents
Going through your trash or stealing from your mailbox is an old-school way for hackers and thieves to collect personal data. Way too many companies send unsolicited offers through the mail. And while it’s annoying, they often put sensitive personal info in the offers as well (I’m looking at you Credit Card companies).
You need to shred those documents before they get shoved into your waste bin. Here are the snail mail documents everyone should shred:
- Anything with your social security number on it
- The same goes for Birthdate
- Credit Card numbers
- Account numbers
- Medical Insurance Number
But, shredding everything you intend to throw out is ok too. I use the adage of “when in doubt, shred.” If you don’t already have one, get yourself a quality paper shredder.
41. Shut Off Unsolicited Credit Card Offers
You won’t miss out, I promise. They don’t send you these offers to “save” you money. They send these unsolicited offers because they make themselves lots and lots of money, at your expense. Plus, they put your personal privacy at risk.
These “offers” can get stolen, filled out by identity thieves, and get the actual Credit Cards sent to their address. Then it’s just a matter of activating them and quickly piling up debt before you notice. And while you’ll unlikely to be on the hook for such damages, it’s a personal privacy security mess.
You can put a stop to many of these unsolicited offers by going to optoutprescreen.com or calling 888-567-8688. This service is run by the Consumer Credit Reporting Industry. If you ever feel like you need more credit, shop around online on your terms, you don’t need these unsolicited offers coming in the mail.
42. Receive Less Mail Overall
What about all those other unsolicited offers? You can reduce those too by up to 80% using dmachoice.org. I also recommend you visit their “Learn More” page first to get an idea of how it all works.
Cyber Security and Privacy Final Thoughts
Odds are, you got so into reading this cybersecurity and privacy guide that you forgot to take action. That’s ok because this is your kick-in-the-pants reminder to go back to the top and slowly work your way through all the action items.
Unless of course, you want to kick yourself later for only doing half the work. Information not put to use is…useless.
Your personal data will thank you.

Prepare, Adapt & Overcome,
P.s. - I just found out 2 out of 3 Americans don’t feel prepared for a 3 day disaster!!!
I guess this goes to show how modern society continues to embrace ‘living a fragile life.’ What’s crazy is… it’s so easy to fix.
To make sure YOU have the basics, watch our FREE training on “10 Simple Steps To Basic Preparedness” that shows you HOW.
Nothing crazy here… this isn’t doomsday prepping... just the basics every responsible adult should have before a disaster strikes.Why You Can Trust Skilled Survival...
Go here now to review a full breakdown of:
- Who We Are
- Our Credentials
- Our Mission
- & Product Recommendations...
Here are a few highlights of our teams credentials & certifications:
- Certified Member of a Mountain Search & Rescue Organization
- Plant Emergency & Safety Leader for a Major Food Manufacturer
- Member of the 10TH Mountain Division Hut Association
- Certifications: Avalanche 1, WFR, CPR
- Official Gear Tester for Numerous Outdoor Gear Companies
- Countless Multiday Backpacking trips into Remote Wilderness
- Bachelor's Degree In Mechanical Engineering
- Bachelor's Degree In Civil Engineering
- Bachelor's Degree In Biomedical Engineering
"It takes 20 years to build a reputation and five minutes to ruin it." - Warren Buffett
We're fully aware that trust is NOT something you GET but is EARNED.
And we'll continue to earn YOUR trust through our forthright and honest approach with each new Blog Post, Guide & Product we create...
P.s - I just took this FREE 60-second 'Readiness Score Quiz'👇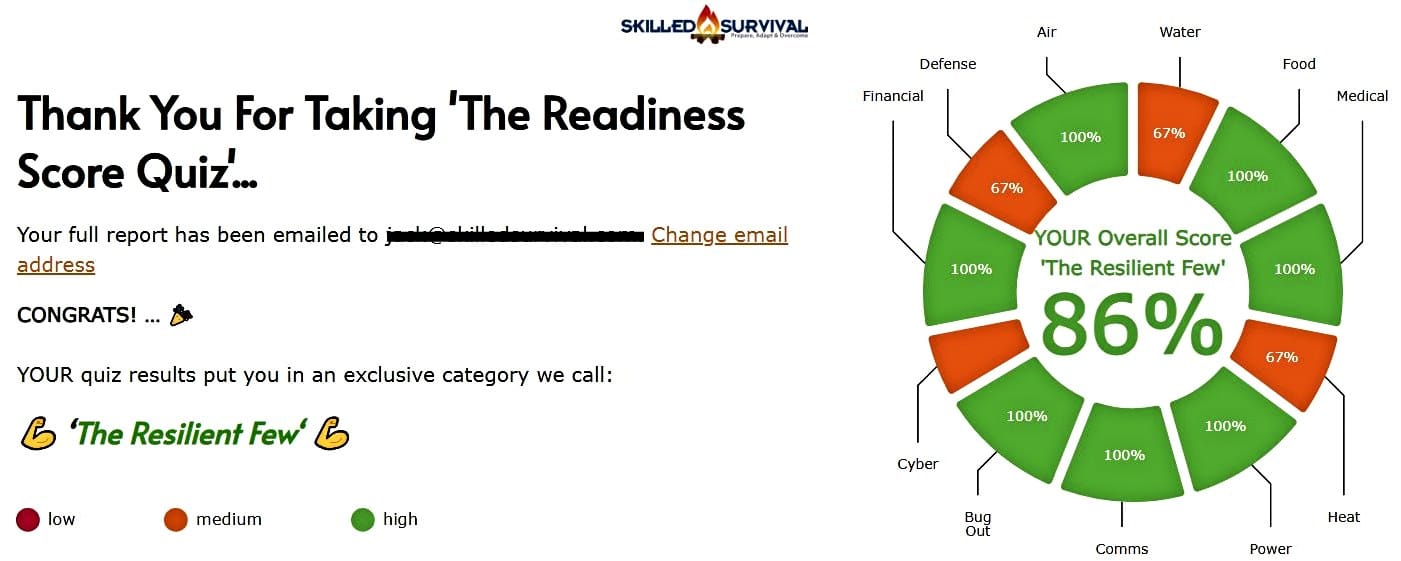
AND... I've still got a few gaps in my preps...🤔 But at least, I'm not part of 'The Fragile Masses'. 👍 Find out where YOU stand by answering a few questions...

Recommended Reading
Long Term Fuel Storage For Survival Emergencies
Long term fuel storage is crucial in emergencies, but fuels must be stored properly especially long term gasoline storage.
How To Store Seeds For Wise Prepping & Survival
When seed saving and seed storage, you must do it right. Learn how to store seeds so they'll thrive the next planting season.
Common Everyday Carry Mistakes YOU Must Avoid At All Costs
The only person qualified to build YOUR Best Everyday Carry (EDC) is YOU. To do it right, you must avoid these common mistakes and pitfalls.
Strategic Relocation: How To Find A Safe Pace To Live
Use strategic relocation to find a safe, defendable location to call home. Your choice of location WILL determine your survival fate.
Nuclear Fallout Map: Would I Survive A Nuclear Bomb?
Have you seen this nuclear fallout map? Or run a nuclear simulation to see the damage a nuke would do to your city? If not, check this out.
Homestead Survival: How To Master Plan Your Safe Haven
Use this simple 6 homestead survival plan to successfully survive (and thrive) even if the world falls into chaos...